
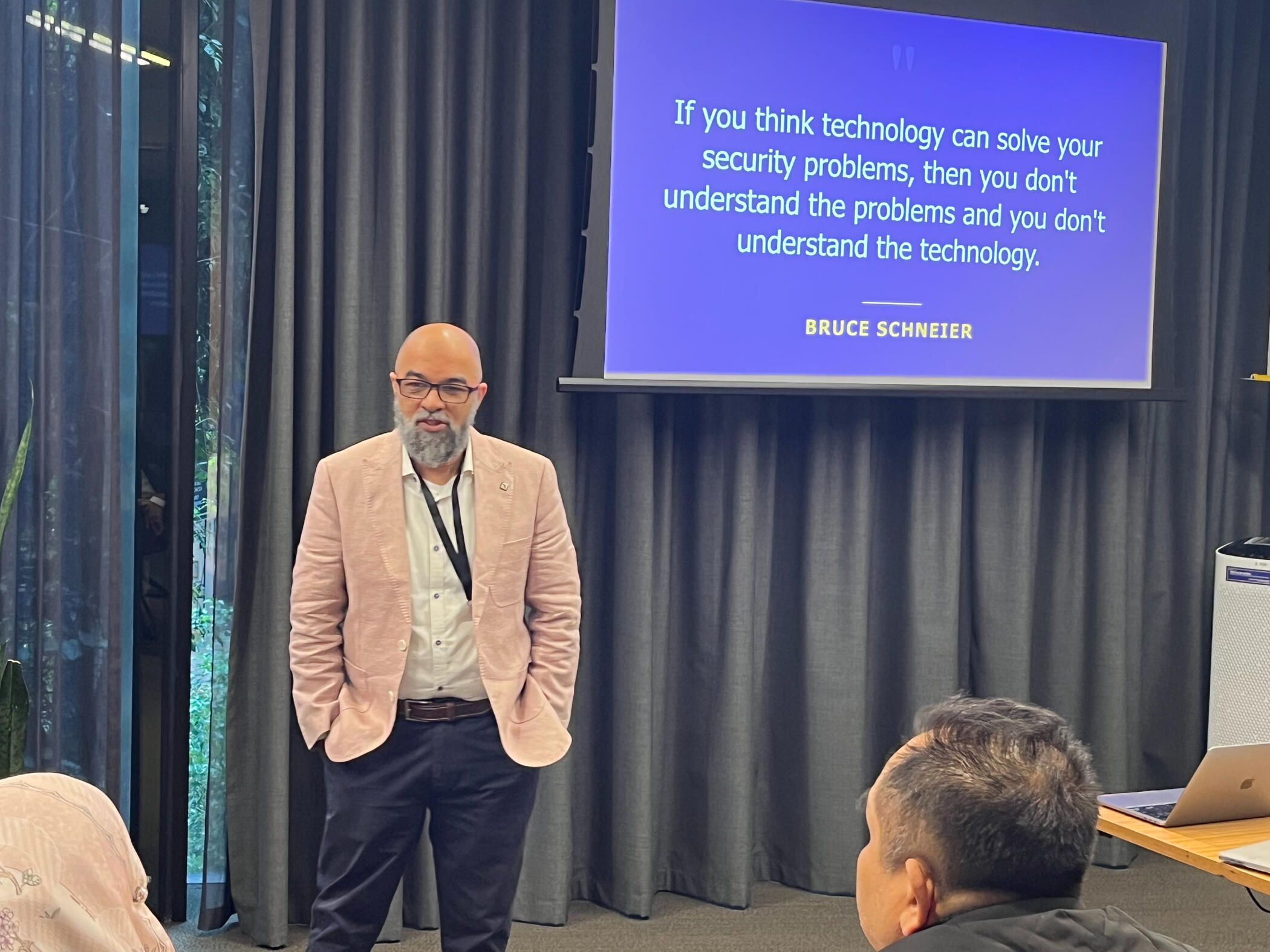
Atif Ahmad
I am a tenured Professor at the University of Melbourne's School of Computing & Information Systems where I serve as Deputy Director of the Academic Centre of Cyber Security Excellence.
What is my research about?
I am a management practice researcher specialising in cybersecurity. I research how organizations behave when they are under cyber attack.
Over a period of 17 years I developed a unique team of Cybersecurity Management researchers drawn from Information Systems, Business Administration, Security Intelligence, and Information Warfare.
Together we conduct case studies, build practice models and train industry executives on how to practice cybersecurity.My research aims to answer the question:How can organizations defend their information resources against organized and sophisticated cyber-threat actors?


Academic Achievements
Professor of Cybersecurity Practice at the University of Melbourne
Deputy Director, Academic Centre of Cyber Security Excellence
Research Metrics
📊 5,000+ citations | H-index 37
💰 $6M+ in competitive research funding
📚 120+ peer-reviewed publications
Recognition & Leadership
🏆 Editorial Board - Computers & Security (5+ years)
🎯 Designated Subject Matter Expert for Malaysia's National Cyber Security Strategy 2025-30
🎬 Award-winning filmmaker - 17 international film festival awards
Industry Impact
🏛️ Government Advisor - Australian DFAT, Malaysian NACSA
🏢 Certified Protection Professional - American Society for Industrial Security (20+ years)
🌏 International Projects - Leading cyber resilience development across Southeast Asia
Research Impact
Transforming Cybersecurity Practice Globally
Capacity Building Projects
🇲🇾 Malaysia: Leading multiple international teams developing national cyber resilience capability
🇵🇭 Philippines Disinformation - Combating information warfare and strengthening digital resilienceSelected Publications
📖 "Situation Awareness for Incident Response" - Computers & Security
📖 "Adopting Cyber-Threat Intelligence" - European Journal of Information Systems
📖 "Strategically-Motivated Advanced Persistent Threat" - Computers & SecurityResearch Translation
🏛️ Executive Training - 300+ government and industry leaders across Southeast Asia
🏢 Industry Adoption - Models implemented by ANZ Bank and Malaysian critical infrastructure

Receiving an Award for Capacity Building Contributions to Malaysia (from Dr Megat, Chief Executive of the National Cyber Security Agency of Malaysia)
Teaching
Award-Winning Education
🎬 17 Film Festival Awards - Including "Best Original Screenplay" at London International Film Festival
🏆 Faculty T&L Engagement Award (2021) - For innovative cybersecurity education
🎯 Coursework Development Excellence Award (2017)
PhD Supervision Excellence
👨🎓 12 PhD Completions - Training industry leaders and academics
👩🎓 13 Current Supervisions - From cybersecurity strategy to national policy
Executive Training Impact
🇲🇾 Malaysian Government - Training 100+ cyber executives and officials
🇮🇳 Indian Industry - Masterclasses for Reliance Industries and tech leaders
🇦🇺 Australian DFAT - Strategic cybersecurity training programs
Innovation Leadership
🎞️ Horizon Film Series - Research-based cybersecurity scenarios used globally

With A/Prof Sean Maynard and Dato' Dr Michael Lim - Directors of Melbourne Security Associates
Connect!
Contact Information
📍 School of Computing & Information Systems
University of Melbourne, Parkville VIC 3010, Australia
📧 [email protected]
📞 +61 3 8344 1396
Professional Opportunities
🎤 Speaking Engagements - Cybersecurity strategy, incident response, regional development
🏢 Executive Training - Government and industry cybersecurity leadership
🤝 Research Collaboration - Cross-disciplinary projects and partnerships
📚 PhD Supervision - Not currently accepting applications
Professional Affiliations
🛡️ Certified Protection Professional - American Society for Industrial Security